Vulnerability Response in ServiceNow’s Jakarta Upgrade
This is the third part of our IT Security Operations series and first look into this new functionality within ServiceNow's Jakarta upgrade, if you have missed the previous blogs click here.
An essential application for maintaining up to date IT/Network security is using a Security Operations instance which can keep itself updated with the latest published vulnerability data (identifying known weaknesses in software/OS, exploitable by malware and other types of attack) using scheduled downloads from NIST’s Vulnerability Database (NVD). Some related abbreviations that you may need to be aware of are;
- CWE (Common Weakness Enumeration) – a common language of discourse for discussing, finding and dealing with the causes of software security vulnerabilities as they’re found in code, design, or system architecture. This applies to the vulnerability – not the instance within a product or system.
- CVE (Common Vulnerability and Exposure) – a dictionary of publicly known information including security vulnerabilities and exposures. This applies to the specific instance within a product or system – not the underlying flaw.
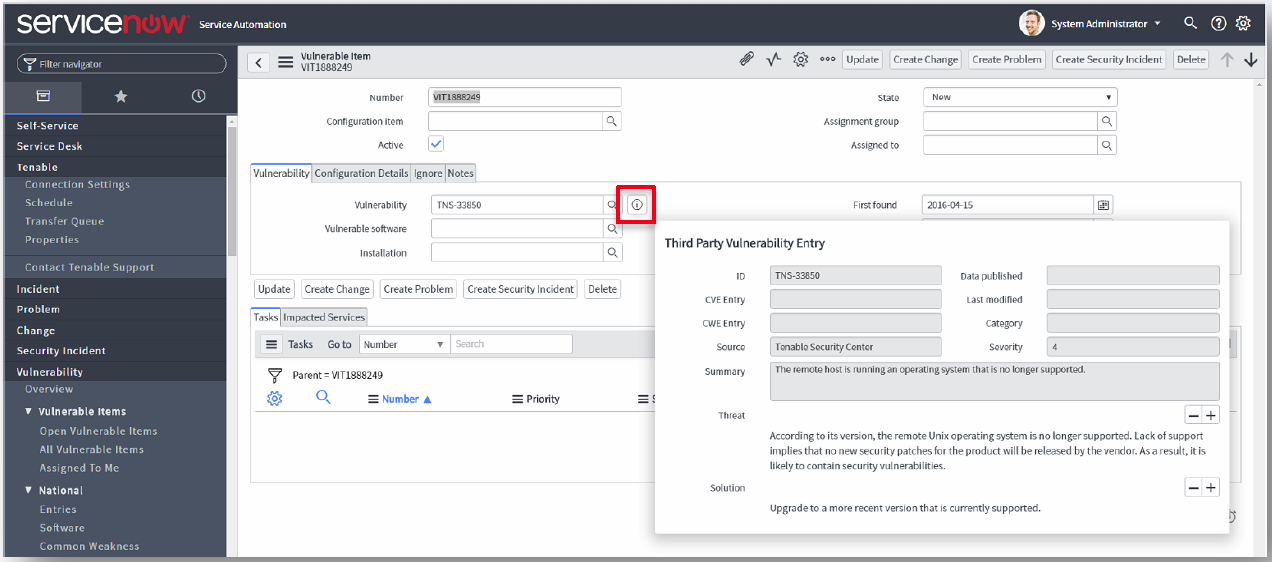
I was pleased to learn that a ServiceNow integration for Tenable’s security center (arguably the most popular scanner used to identify vulnerabilities out there) is readily available from ServiceNow’s app store, enabling remote control via the ‘MID’ server option. This feature allows you to schedule vulnerability scans and import the results into ServiceNow, identified as ‘vulnerable items’ that clearly identify the ‘source’, ‘summary’, ‘threat’ and ‘solution’ for your security operations team. By doing so, this ensures a timely response for support teams to remediate the list of discovered ‘vulnerable items’ (as related to CWE’s and CVE’s) in order of priority!
Threat Intelligence
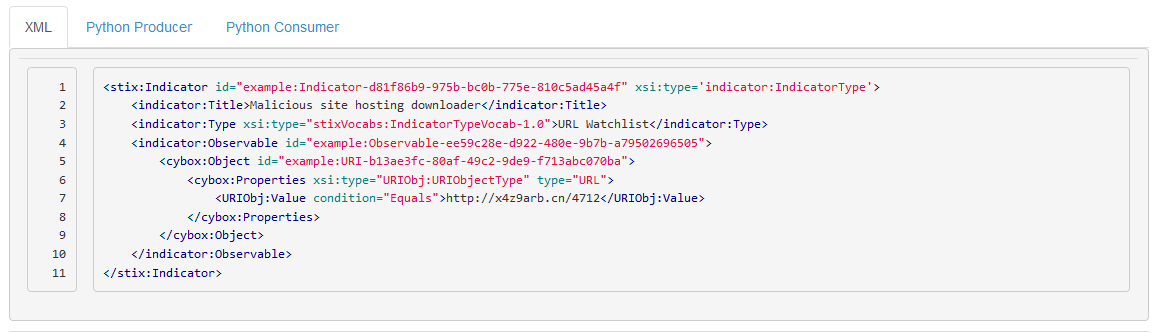
This application provides your organization with an internal point of reference to support the analysis and sharing of cyber threat intelligence data defined using the STIX (Structured Threat Information eXpression) language - see https://stixproject.github.io/about. Sorry for yet another acronym, not one you’d normally hail on the street is TAXII (Trusted Automated Exchange of Indicator Information), a free and open transport mechanism that standardizes the automated exchange of cyber threat information. Click here for further information. https://taxiiproject.github.io/about
The term ‘STIX idiom’ is used to define an instance of threat intelligence for a specific use case e.g. an indicator for a malicious URL can be seen in the example below. If incoming event data matching this malicious URL is received by your instance, this information is at your disposal to help determine the next steps – whether this requires manual operator interaction or automated response using ServiceNow’s automation features.
That’s it for this week’s blog, next week I will be writing about the new 'Trusted Circles' functionality.
If you have any questions in relation to this blog post or wish to find out more about us, feel free to contact us on the links below.
- Contact us:
- 0800 783 3040
- info@engage-esm.com
