Feeding events into Security Operations in ServiceNow’s Jakarta

Welcome to the first instalment of our IT Security Operations blogs; with the release of ServiceNow’s latest upgrade Jakarta, I’m interested in the benefits that the new functionality offers our security conscious customers (hang on a second, aren’t we all more security conscious individuals in today’s evolving IoT; that’s plagued with botnets, infested by malware and trained black-hat hackers looking for some fun! I think a big YES is the answer to that – if it’s a no, then you should be!)
A personal note – we’ve probably all provided our parents with a few tips to help keep their home IT secure (My father is a 75 year old retiree who had no opportunity for IT training way back in the 1950’s). My favourite example was; “No DAD stop! Don’t log in to PAYPAL and change your password when you’ve received what appears to be a perfectly valid email” (as apparent to him), that looks completely suspect (to me, since I could see he was being directed to www.paypol.com...easy mistake to make when you have poor eyesight!). I avoided trying to explain the term ’phishing’ to him at that time seeing as it would only cause more confusion!
Anyway back on topic, time to convey the headline features of ServiceNow’s Security Operations that really grab my attention! The truth is there’s a whole host of new security related functionality in ServiceNow's Jakarta release that’s not only relevant to exisiting ServiceNow users but also for those organizations with existing Security Operations tools looking to up their game. In any case, I’ll give you my take on Jakarta by talking through some real examples…
Feeding Events into Security Operations
First task, I need to get events from my enterprise’s SIEM tools such as firewalls (e.g. Palo Alto), DDoS Protection (e.g. Arbor APS), event monitoring (e.g. Splunk, HP OMi) fed all the way up into my shiny new Security Operations instance hosted up in the cloud. This can be achieved with the Event Management application which offers a number of different methods; the most popular being a ‘MID’ server deployed on-premise that acts as a secure gateway.
The MID server supports a wide variety of event listeners; SNMP Trap, syslog and Web services; SOAP/RESTful, with many connectors readily available for popular tools like those mentioned above, and Microsoft SCOM, Tanium and Elastic may come in handy. Security Operations can also be called to action via inbound email notifications and IoT device (e.g. sensors, smart meters) ready connectors to Amazon AWS or Microsoft Azure.
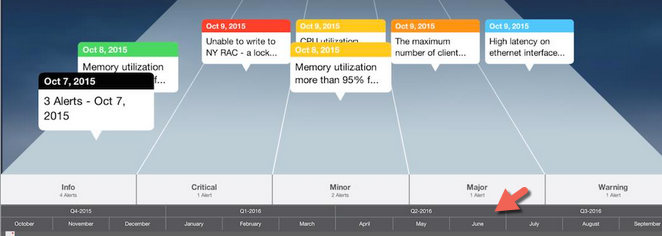
Once your Security Operations instance starts receiving events, your ‘event rules’ are consulted to determine what automated action(s) it should take, such as transforming the raw event data contained within these events. to create meaningful Alerts for remediation and tracking.
Before we move on, I must admit that I like ServiceNow’s Alert timeline view, which is a very useful feature to add to my inventory. I’m pretty sure the person who devised this got the idea from the scrolling star wars movie prologue. ![]()
Right, you get the picture! I’ll stop there and next week we will move on to Security Incident Response.
If you have any questions in relation to this blog post or wish to find out more about us, feel free to contact us using the links below.
- Contact us:
- 0800 783 3040
- info@engage-esm.com